Setting up Scalr & Azure DevOps Part 1 - Picking a Workflow
Learn how to use Scalr with Azure DevOps Part 1
This post is part of a series on CI/CD and GitOps for Terraform & OpenTofu.
This was written by Jack Roper, a guest blogger.
To get started using Scalr with Azure DevOps, there are 3 initial stages to go through. In this series of 3 posts on using Scalr with Azure DevOps, I will walk through each stage step-by-step.
This first post in the series will focus on stage 1 — picking a workflow.
Post 2 in the series will describe how to add Azure credentials and link them to an environment.
And finally, post 3 in the series will focus on how to execute your Terraform code and create a workspace, both using PR automation, and by plugging the CLI into Azure DevOps. There is a third way to create a workspace using the module registry as well, but this still uses the VCS connection.
Let's go!
What is Scalr?
Scalr is Terraform Automation and Collaboration (TACO) software that has support for pull request automation, native Terraform CLI, or module-driven workflows. Scalr helps organizations of all sizes scale through its hierarchical model that centralizes admin operations like RBAC, policy control through OPA, operational views, and a private module registry, resulting in controlled decentralization of Terraform operations allowing developers to execute Terraform workflows within environments independently.
Also from https://docs.scalr.com/en/latest/introduction.html:
Scalr is a remote operations backend for Terraform. What does this mean in basic terms? It executes Terraform operations and stores state, regardless of the workflow, in Scalr itself allowing for easy collaboration across your organization. That means you can easily onboard an existing GitOps or native Terraform CLI based workflows into Scalr with little to no modification to your actual code.
Getting Started
The 2 ways to get started with Scalr depending on your workflow are:
- Adding the Version Control System (VCS) provider, in this case, Azure DevOps.
- Using the Terraform CLI in the Azure DevOps pipeline.
Authenticate to Scalr with Azure DevOps
First, we will need to choose the project in Azure DevOps you want to link with Scalr. I've set up a test one:
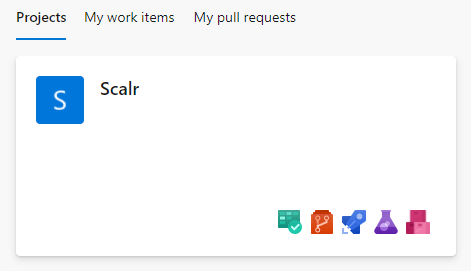
Inside my Project, I have a repo called Scalr with some basic terraform files. When applied the configuration will create a given number of Azure AD Groups.
main.tf
provider "azurerm" {
features {}
}
terraform {
required_providers {
azurerm = {
source = "hashicorp/azurerm"
version = ">=2.95.0"
}
azuread = {
source = "hashicorp/azuread"
version = ">=2.17.0"
}
}
backend "azurerm" {
// resource_group_name = "tf-rg"
// storage_account_name = "jacktfstatesa"
// container_name = "terraform"
// key = "adgroups.tfstate"
}
}
resource "azuread_group" "ad_group" {
count = 3
display_name = var.ad_group_names[count.index]
security_enabled = false
mail_enabled = false
}variables.tf
variable ad_group_names {
type = list(string)
description = "List of all the AD Group names"
}terraform.tfvars
ad_group_names = ["Group1", "Group2", "Group3"]Setup the Azure DevOps integration using the web interface
Scalr can Integrate with several VCS providers to automate your GitOps workflow. Let's run through setting it up with our Azure DevOps repo step-by-step!
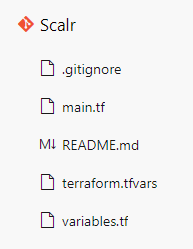
When you first log in to your Scalr account, you will be greeted with the following:
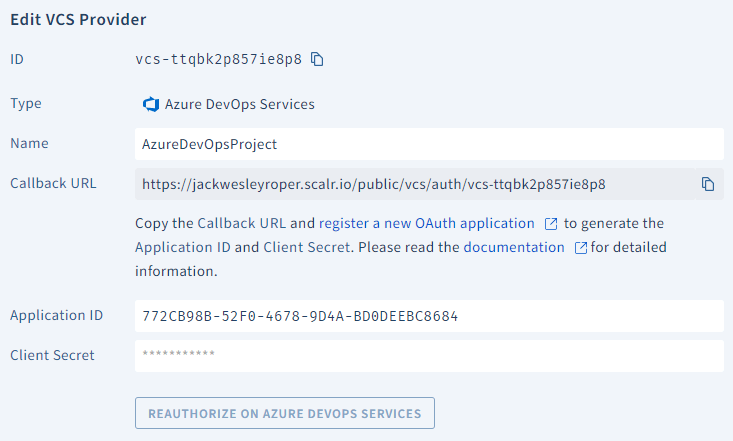
Clicking on 'create VCS provider' and then 'Azure' presents the following options:
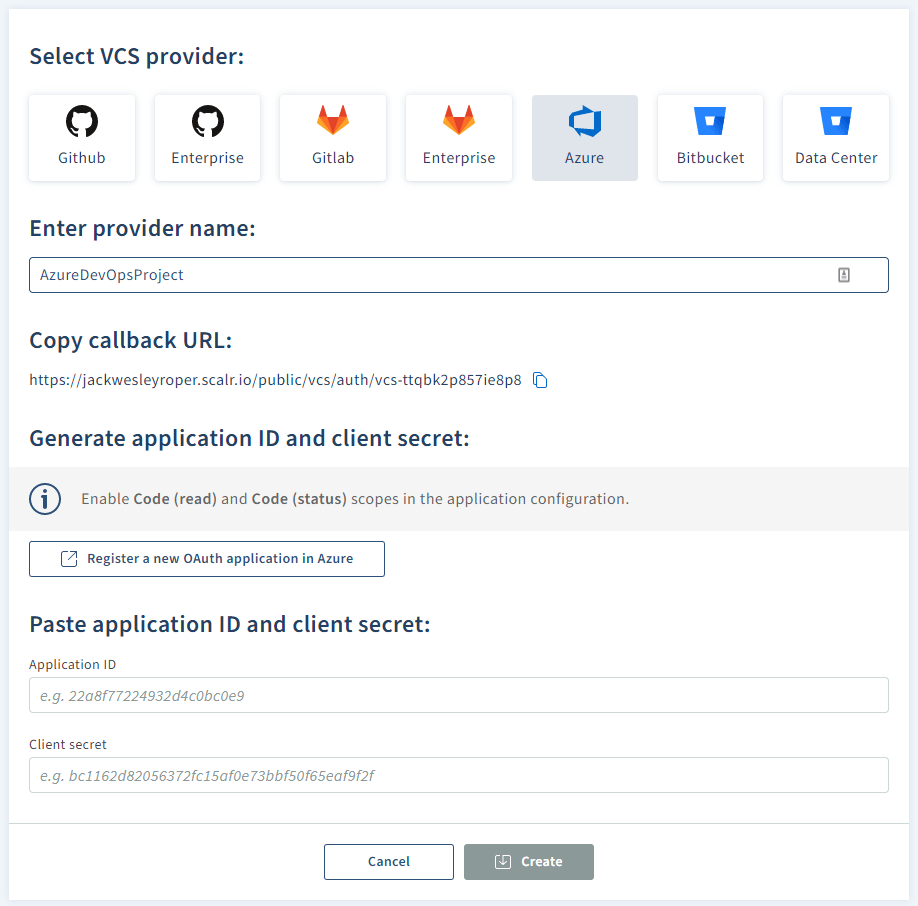
- Enter your provider name (e.g. AzureDevOpsProject)
- Hit the 'Register a new OAuth application in Azure' button, it will take you to register an App in Azure DevOps — https://aex.dev.azure.com/app/register
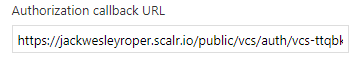
- Copy the callback URL and paste it into the Authorization callback URL in the Azure DevOps page
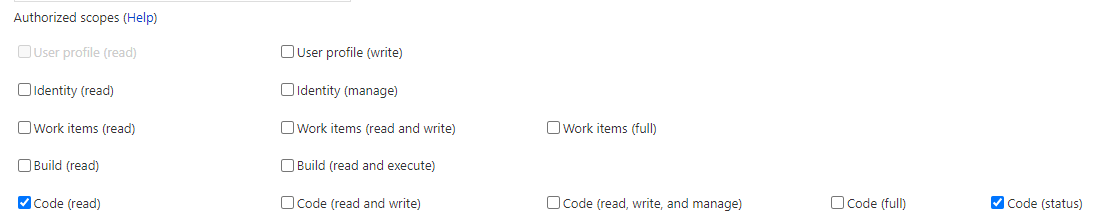
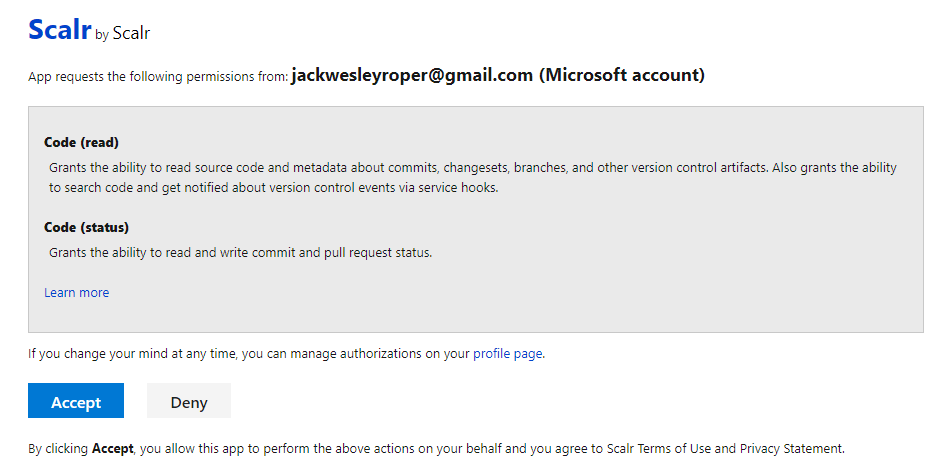
- Under authorized scopes, tick code (read) and code (status).
- Fill in the company name, Application Name, and Application website fields, then hit 'create application'. Your application settings will be presented:
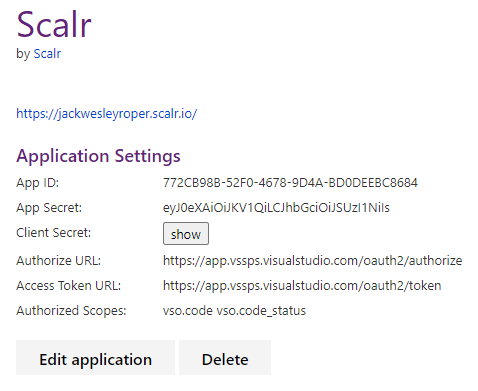
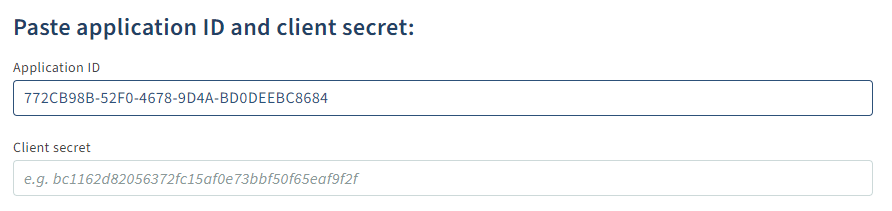
- Back in Scalr, paste your app ID and client secret and press 'create':
- Hit accept:
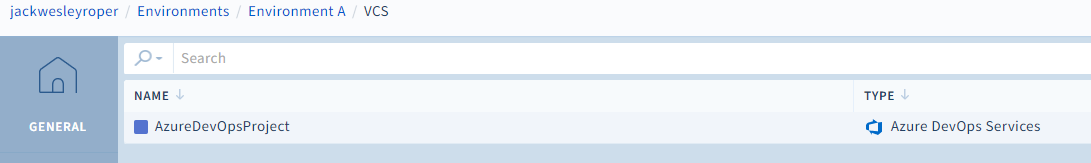
- Scalr will now show the Azure DevOps is connected.
Authenticate to Scalr with the Terraform CLI
If an existing workflow already exists that utilizes the native Terraform CLI or you just want the flexibility to use it, you can continue to use the Terraform CLI as it is fully supported in Scalr. Scalr will execute the runs in a container in the Scalr backend, but the logs and output will still be sent back to your console. To utilize Scalr as a remote backend there are a few simple steps:
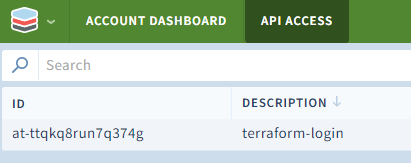
- Obtain an API token by running
terraform login <account-name>.scalr.io - Create a workspace
- Execute
terraform init
terraform login jackwesleyroper.scalr.io
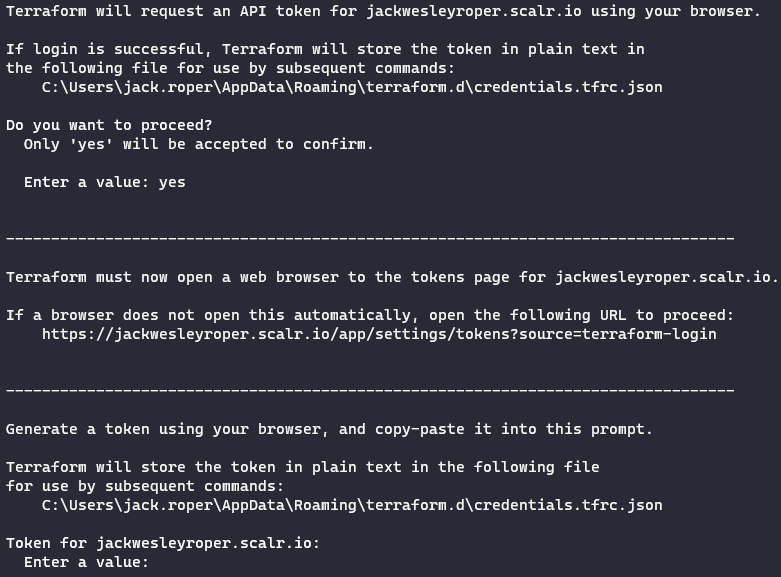
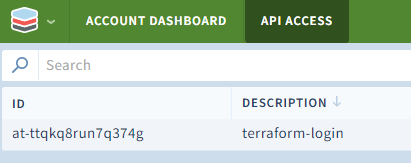
Press 'Create API Token', then copy the resulting ID and Token.
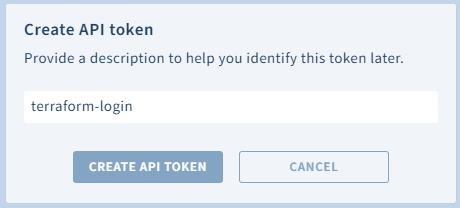
The token should be displayed in Scalr.
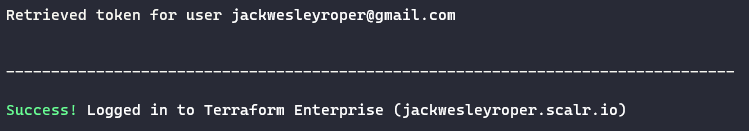
Paste the token back into the command window:
The Scalr Terraform Provider
Note that the Scalr Terraform provider can be used to manage the components within Scalr. This will allow you to automate the creation of workspaces, variables, VCS providers, and much more.
Summary
We have connected our VCS provider, (Azure DevOps) to Scalr and also shown how to Authenticate to Scalr with the Terraform CLI.
Next part 2 in the series on Scalr will look at how to add Azure credentials and link them to an environment.
Cheers! 🍻