Setting up Scalr & Azure DevOps Part 3 - Add Azure credentials
Learn how to authenticate with Microsoft Azure using Scalr provider credentials. Part 3.
This post is part of a series on CI/CD and GitOps for Terraform & OpenTofu.
This was written by Jack Roper, a guest blogger.
To get started using Scalr with Azure DevOps, there are 3 initial stages to go through. In this series of 3 posts on using Scalr with Azure DevOps, I will walk through each stage step-by-step.
This is the second post in the series that will focus on stage 2 — how to add Azure credentials and link them to an environment.
If you missed the first post in the series, check it out here — picking a workflow.
And finally, post 3 in the series will focus on how to execute your Terraform code and create a workspace, both using PR automation, and by Plugging the CLI into Azure DevOps. There is a third way to create a workspace using the module registry as well, but this still uses the VCS connection.
Provider credentials
In order to authenticate with our cloud provider (Microsoft Azure), we need to provide Scalr with some credentials. Credentials can be stored in Scalr in a central location, enabling you to share them across workspaces. They can also be shared across environments, but there can only be one set of credentials per provider type for each environment (I've been told this limitation will be removed very soon and multiple credentials for the same provider will be able to be added to each environment). The credentials are encrypted and are stored securely. Credentials are passed to all workspaces in the environment as shell variables. By doing this, the team can restrict who actually has access to the credentials and all new workspaces will automatically inherit them making management of credentials very easy.
In this post, we will also show how to create the necessary credentials in Azure as an Azure Active Directory app registration, and assign it an appropriate role.
As we will be using Terraform with Scalr to deploy infrastructure to Azure, in the third and final post of the series, we will show how when a Terraform run is executed within a workspace, the provider credentials are automatically passed to the run as a shell variable.
Adding Credentials to Scalr
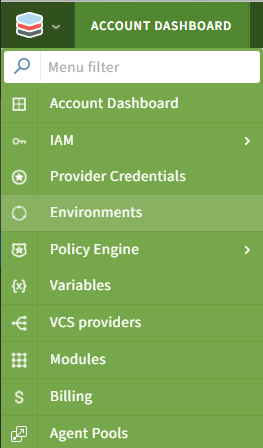
- Log into Scalr and hit the icon top left. Select 'Manage Account' in the drop-down menu.
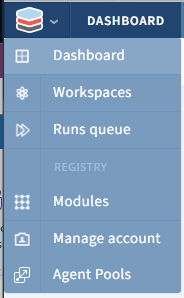
- If this is the first set of credentials you will be adding, you will be presented with the 'getting started' screen, and the 'add cloud credentials' button.
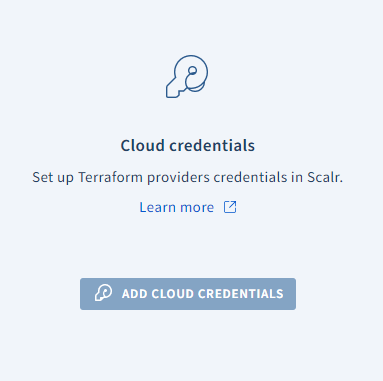
Alternatively, if you already have credentials added, hit the icon top left again, and select 'provider credentials' from the drop-down.
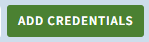
- Choose 'add credentials' then choose the Azure provider from the drop-down menu. Note that if you want to use a provider that does not have an option in Scalr, you can use the shell variable option to achieve similar functionality.
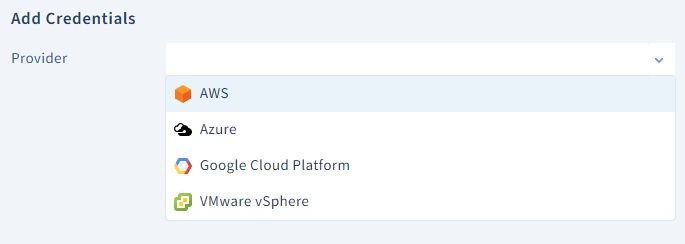
- At this point jump over to the Azure portal and log in to your account. Click on Azure Active Directory → App Registrations.
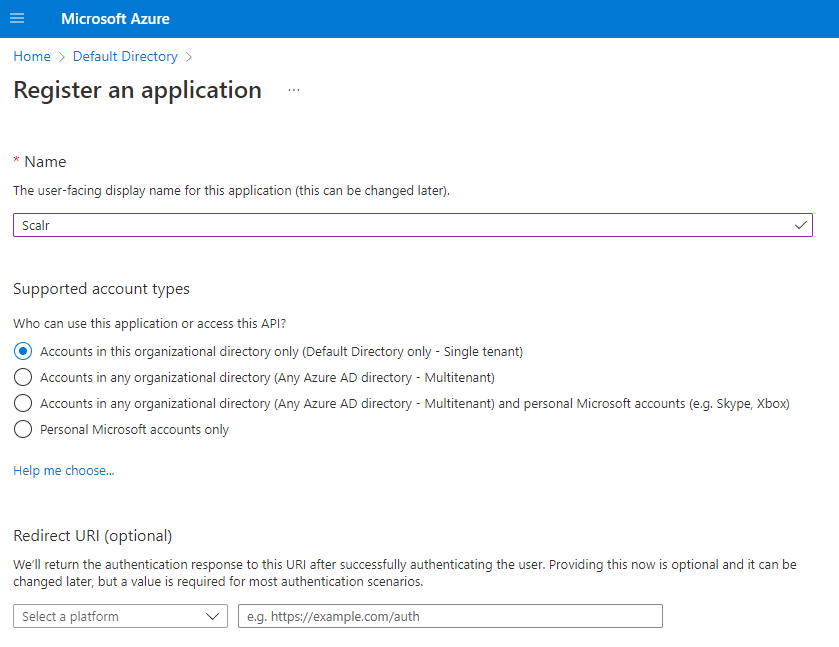
Press register. On the next screen copy the details shown in the essentials section.
Next click on secrets -> new client secret
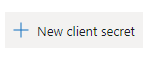
Enter the description and the expiry date.
Press add, then copy the secret value. You will only be able to see this once.
Next, we need to give the app registration permission to the Azure Subscription we want to use with Scalr. Browse to your subscription, and click on Access Control (IAM).
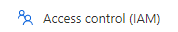
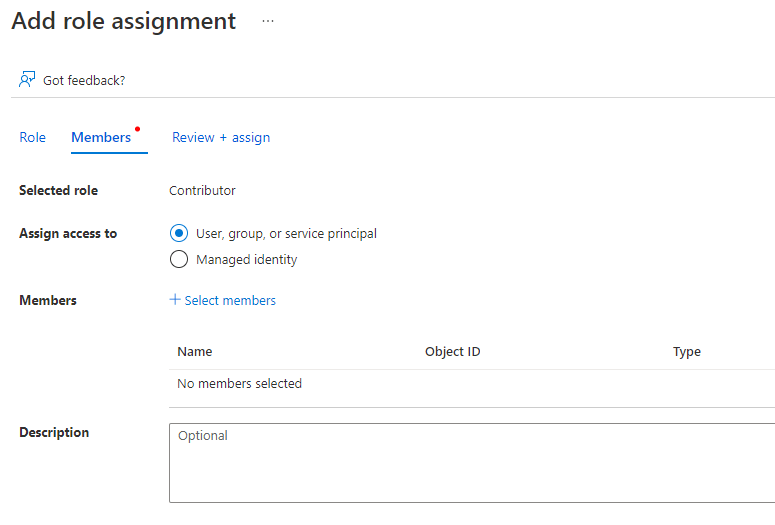
Click role assignments, then add -> add role assignment.
Here I choose contributor (has full access to the subscription but cannot change permissions) then hit next.
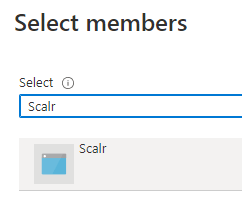
Choose 'Select members and in the search bar type the name of the app registration you set up earlier.
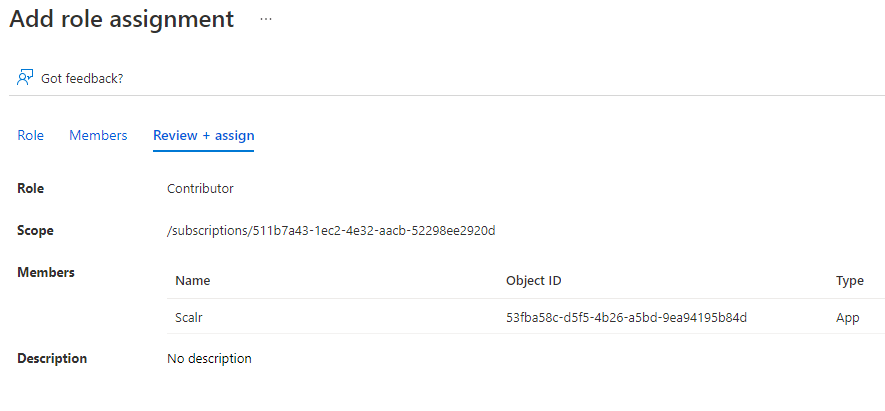
Press select, then review & assign.
- Back in Scalr, add the details you copied from the app registration:
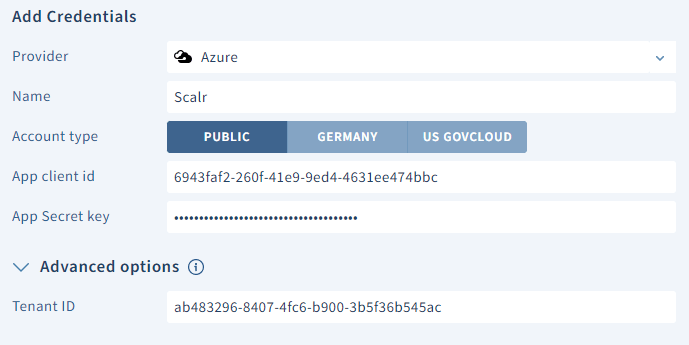
Press save. If the connection is successful, your subscription will show in the drop-down subscription menu. Select it and press Save.
- Link the provider credentials to the required environments by clicking on the Scalr icon top left, then environments.
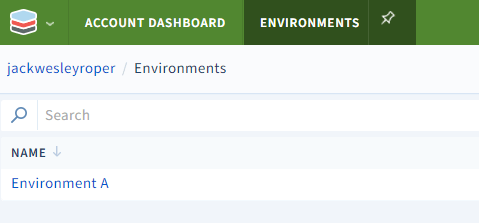
Select the environment, and then the Provider Credentials tab.
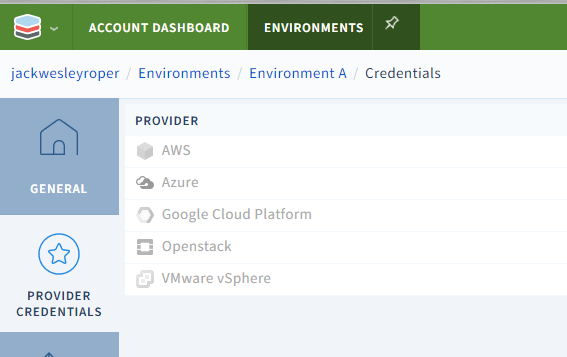
Across from the Azure provider, hit Link, then select the tickbox next to the provider credential we created earlier.
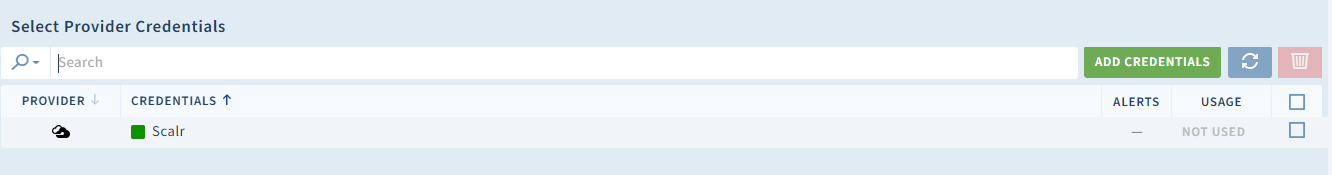
Lastly, press save!
Summary
In this post, we have shown how to create an App Registration in Azure, assign it a role in the subscription, and successfully add it to Scalr as a provider credential. We then linked the provider credential to the Scalr environment.
In the previous post, we linked Scalr to our Azure DevOps VCS provider.
In the next post, we will execute some Terraform code to deploy infrastructure to Azure!
Cheers! 🍻