Your costs = usage. Period.
Do you use more than one Terraform provider? We sure hope you do, so read on, friend!
At Scalr, we’re on a mission to provide you with a great alternative to Terraform Cloud. This Summer we went beyond it, releasing an important feature that facilitates managing the configurations of all the providers you use, supports role delegation, and makes them easy to reuse across workspaces.
We’re calling the feature Provider Configurations, ‘cause we’re a creative bunch.
If you’re anything like me, you’ve got dozens of services managed via Terraform, from AWS to DNS to Kubernetes to AzureAD to VMware, perhaps even hundreds! See the top 20 providers here. That’s a lot of configurations. Managing who has access to each, rotating keys, and keeping things secure can be a grueling task.
Provider Configurations makes this easy. You write Terraform code to manage the configuration of each provider, and from the same place, define which environments and which workspaces can use the configuration. Here’s some sample code to let a “dev” environment use an AWS configuration.
As you can tell from the code, this makes it super easy to manage the secrets needed by your providers.
Provider configurations are a first class citizen in Scalr, allowing you easily manage, share, and scale access to hundreds or thousands of configurations of Terraform providers across the organization, and is the first of many ways in which we’re going beyond Terraform Cloud to create an amazing collaborative platform to centralize administration while decentralizing operations.
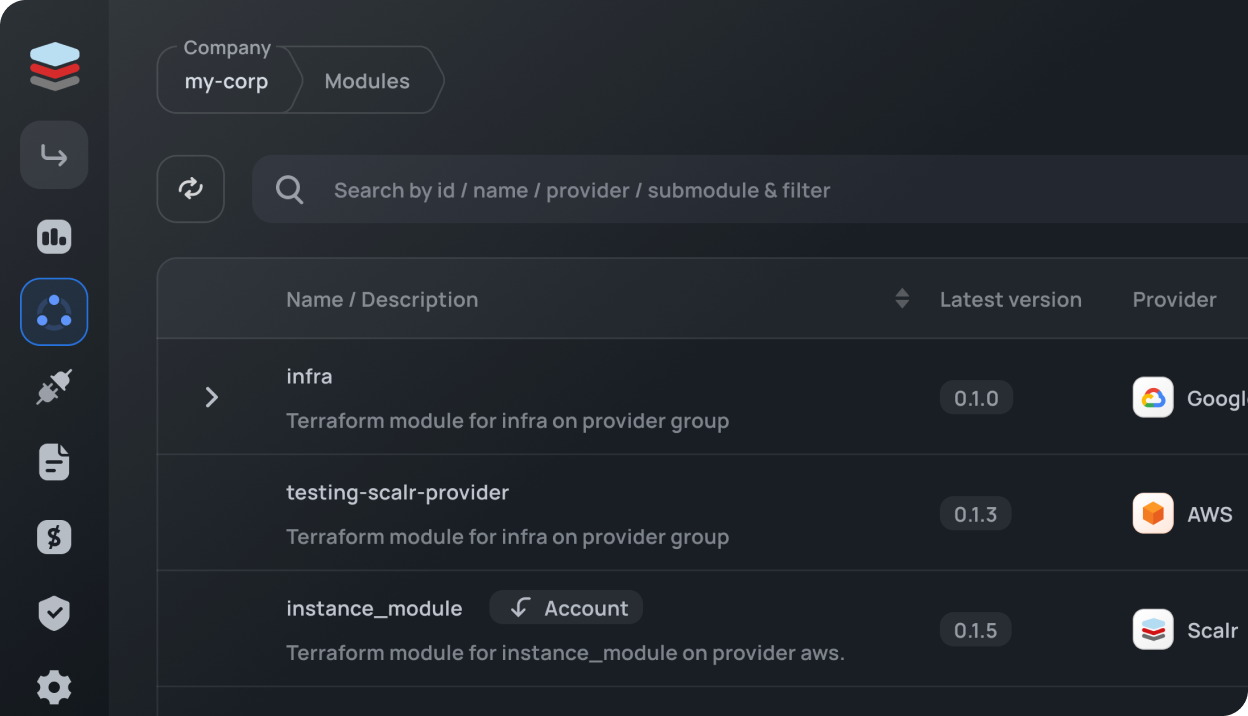
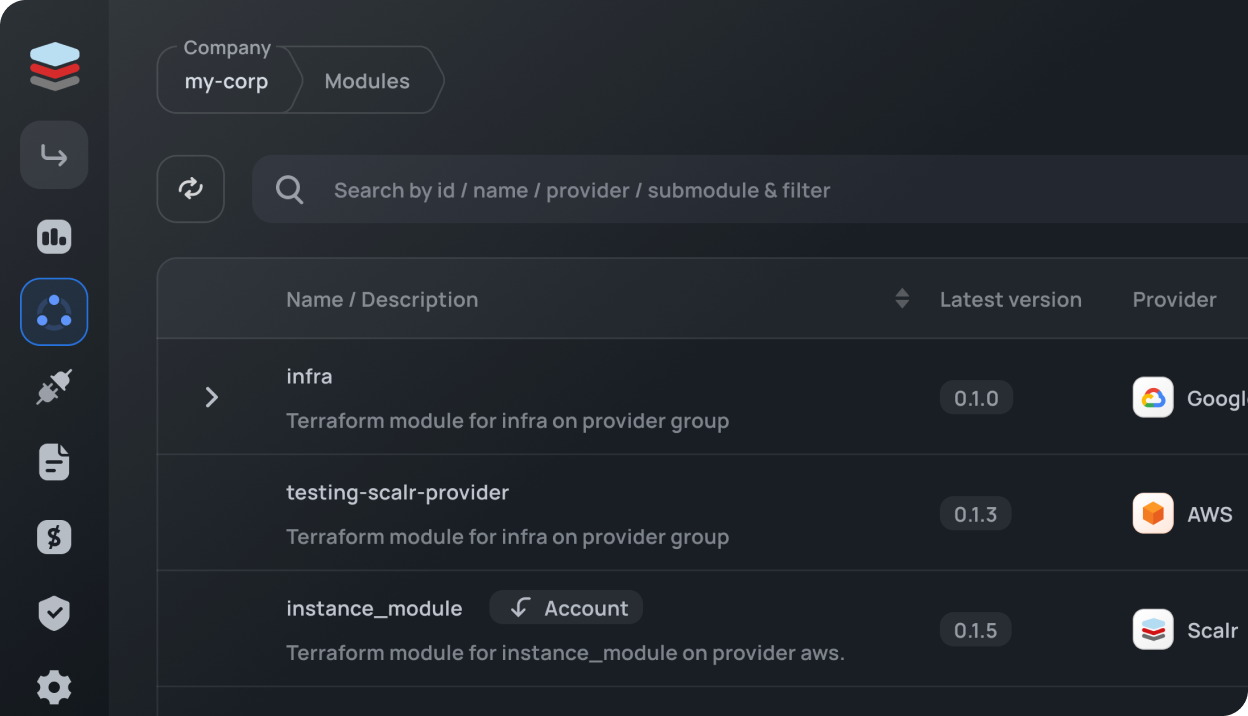
Today, Provider Configurations are available in the API, so we recommend using the Scalr provider to get started. If you prefer a web interface, use the following link after substituting your account name and id: https://<account-name>.scalr.io/app2/a/<account-id>/provider-configurations